The UK Government should protect encryption not threaten it
Encryption also strengthens democracy by underpinning digital press freedom. Whistleblowers can’t safely reveal official corruption to journalists without it.
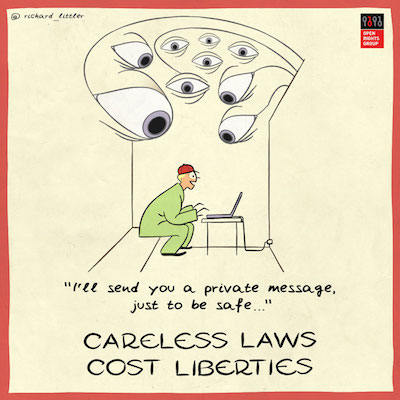
Laws restricting encrypted communications have generally been associated with more authoritarian governments, but lately proposals to circumvent encryption have been creeping into western democracies. Former Prime Minister David Cameron attacked encryption after the Paris attacks in 2015, and Home Secretary Amber Rudd MP recently said that there should be a way around end-to-end encryption on devices like WhatsApp.
As it happens, Amber Rudd already has legislation that claims to give her the power to tell WhatsApp to remove “electronic protection” (read “encryption”). She can issue a technical capability notice (TCN) which instructs commercial software developers to produce work-arounds in their software without outlawing or limiting encryption itself. Just over a week ago,
